What are DKIM Records and why you should use them?
Let’s simplify this down by looking at DKIM records as a Lock and a Key. A DKIM signature in your email header is essentially the “lock” and your DKIM record acts as the key. Your DKIM record is a published string of characters in your domain’s DNS records. These can only be generated by an email admin an can only be added by your domain administrator (click here for more information on DNS Management). If Spotlight Studios administer both your email and domain we can manage the process on your behalf.
How does DKIM work?
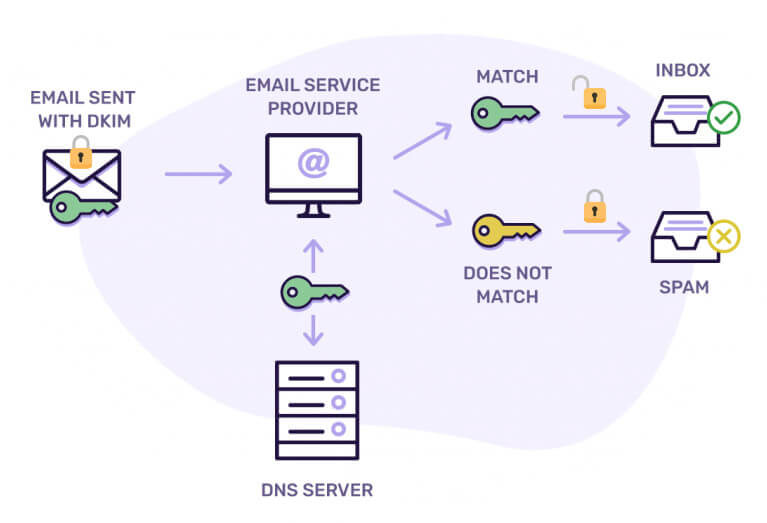
When an inbound mail server receives a message, it will detect the DKIM signature (aka padlock) and look up the sender’s public DKIM key via their DNS. The variable or DKIM selector provided in the DKIM signature is used to determine where to look for this key. If the key is found, it can be used to decrypt the DKIM signature. This is then compared to the values retrieved from the received mail. If they match, the DKIM is valid, if not then this is either rejected or filtered (depending on the rules of the receiving server).
How does is tie in with other standards?
The “other standards” often covered within the same context as DKIM are SPF and DMARC records. All these standards contribute towards different aspects of email authentication and address complementary issues:
- SPF allows senders to define which IP addresses are allowed to send mail for a particular domain.
- DKIM provides an encryption key and digital signature that verifies that an email message was not faked or altered.
- DMARC unifies the SPF and DKIM authentication mechanisms into a common framework and allows domain owners to declare how they would like email from that domain to be handled if it fails an authorization test.
Why should I used them?
If you are a business sending commercial or transactional email, you definitely need to implement at least one or more forms of email authentication to verify that an email is actually from you or your business. In most instances an SPF record will be more than sufficient however properly configuring email authentication standards is one of the most important steps you can take to improve your deliverability. If your business works in the financial sector you may find more instances where emails are rejected if they do not have a more “complete” email authentication policy. Where websites are involved where ensuring customers receive important automated correspondence then transactional mail is an important add-on which provides the next level of deliverability options.
Email Provider Help Articles
- Google – Help prevent spoofing and spam with SPF
- Google – Turn on DKIM for your domain
- Microsoft – Set up SPF to help prevent spoofing
- Microsoft – Use DKIM to validate outbound email sent from your custom domain
You may also find this post interesting: Combining SPF Records for Domain Authentication
Has something in this article peaked your interest? We’re never more than a few clicks or a quick call away so please don’t hesitate to get in touch!



